Cyber Crime – Cyber Security
No matter what size your company is, no matter what industry, no matter what countries you operate in: Your company is the target of cyber criminals. The compliance office in particular is often a worthwhile target for attack, especially in the financial industry. A wealth of internal and external data flows together here, e.g. in trade surveillance, but also in the monitoring of employee transactions or the initiation of M&A activities. Often this includes highly sensitive data from day-to-day business, customer data as well as employee data. In the event of a data leak or data manipulation, there is the threat of incalculable headline risk, in addition to high penalties that can also be imposed on individuals.
The compliance office must constantly rethink and reformulate its requirements, especially its risks with regard to security. Especially now, when due to the pandemic many meetings take place virtually, often even in the home office. Entire business processes are suddenly outside the previous IT landscape, and further worthwhile points of attack have opened up for criminals.
“On March 20, 2013, there was a cyberattack against South Korean banks and television stations. At the same time at around 14:00 (6:00 CET), massive network disruptions occurred. South Korea’s Ministry of Defense in Seoul raised the cyber threat alert level to three on a five-point scale.”
Source: Wikipedia
Another issue that will become increasingly important in the future is the further increase in automation of business processes. So-called robots are already playing a very large role in some areas of business today. Robo-advisers, chatbots, even copbots – the “cops” that detect fraudulent transactions – are already in use. Next, AI, or Artificial Intelligence, is being applied in more and more areas. Make sure you pay attention to whether supervised or unsupervised systems are planned or already in use here, in machine learning. This is a highly exciting question, especially for the lawyers among you. Think of Tesla and autonomous driving.
After that, however, no, already while these systems are being created, robots will also enter the market on the customer side. Google, Facebook, Amazon will provide customers with powerful AI systems. More and more, IT specialists will be the only ones who can still see through and optimize these processes.
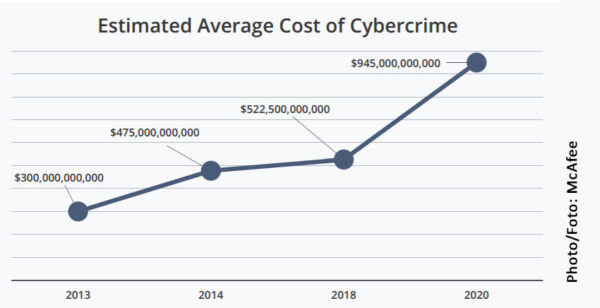
And another bad news: we will see more and more criminal activities from the direction of IT. Your own, at suppliers, at customers, at partners. So you should also consider and develop IT forensics as a very serious, future-oriented compliance task area. The bank robbers of the past have continued their education, trained by the best experts available. You have to keep up with that.
“At the end of April 2021, the food retailer Tegut was troubled by a cyberattack, which caused empty shelves due to the failure of the merchandise management system.”[21] As a result, company data was published on the Darknet by the hackers.”
Source: Wikipedia
In this problem, communication is very difficult for the very reason that specialist departments with very different orientations have to exchange information, also in the respective specialist language. Lawyers, traders, IT experts, data protection officers, security officers, forensic experts, the management.
The number of potential points of attack is high, as is the number of forms of attack. How can the attacks be carried out? Where can the attackers penetrate which systems? What is the goal of the attacks – data theft, data manipulation, spying, denial of service, extortion? Since criminals are constantly working on refining their methods, compliance, just like all other areas of a company, requires regular review and further development of security measures. And the definition, revision of far-reaching decisions in IT policy. One of the most frequently asked questions, loosely based on Shakespeare: cloud or not cloud?
“At the beginning of June 2021, there were massive DDoS attacks on data centers operated by Fiducia & GAD IT, the IT service provider for the Volksbanken, Raiffeisenbanken, and other companies in the cooperative financial group in Germany. They led to temporary outages of online banking.”
Source: Wikipedia
From my point of view, there are many, many arguments in favor of the cloud. Whereas it used to be inconceivable to store and process security-relevant, business-critical data such as that of the compliance office outside the company, the world has changed decisively here.
For cloud providers, security is the core of their business model. The costs here are correspondingly high, but so is the expertise. In principle, therefore, a cloud solution is the obvious choice. But here, too, the costs on the company side should not be neglected. It requires well-trained employees so that the next point of attack does not arise here. In your own system!
Don’t be afraid to address these points openly and persistently in your organization – and to work through them in a structured manner. The costs of doing so are always lower than the consequences of capital errors.
The author is co-founder and CEO of b-next holding AG. He is one of the pioneers and veterans of the RegTech industry with more than thirty years of experience in the sector.

